Categories: Licensing
Stateless Apps, Stateful Licenses: A Strategic Guide to Containerized Protection
The rise of containerization has fundamentally altered the software delivery lifecycle. For Independent Software Vendors (ISVs), the transition to Docker and Kubernetes offers significant scalability advantages. However, it also introduces what can be described as the Containerization Paradox: containers are ephemeral and stateless, while traditional licensing is rooted in persistent hardware binding.
To bridge this gap, technical decision-makers are advised to move beyond "local" activations and architect a licensing strategy that respects the nature of the container.
The Implementation Landscape: A Scenario-Based Map
A one-size-fits-all approach is rarely effective in containerized deployments. The following map helps align your infrastructure with the correct CodeMeter architecture.
| Deployment Scenario | Recommended Architecture | Strategic Rationale |
|---|---|---|
| Public Cloud / SaaS | CmCloud / CmCloud Lite | Complete hardware decoupling; identity-based Licensing. |
| Private Cloud (On-Prem) | CmDongle or Network Server | Centralized entitlement management within a customer’s secure LAN. |
| Air-Gapped Environments | CmDongle or Local Network Server | High-integrity protection without external "heartbeat" requirements. |
| Edge & Industrial OT | Host-Bound / CmASIC / CmDongle | Physical host as a root of trust for containerized logic. |
Implementation Landscapes
Quick Wins: SmartBind – Local Binding in Docker
In the early stages of container adoption, many ISVs attempted to run the CodeMeter Runtime directly inside the container using SmartBind. While this is an attractive "low-effort" path for a Proof of Concept (PoC), it may prove technically fragile in production environments.
The hardware fingerprints that SmartBind relies on (MAC addresses, CPU IDs, disk UUIDs, etc.) are often abstracted or virtualized by the Docker engine. In a containerized context, these identifiers can become less reliable. If a container is rescheduled to a different node in a cluster, the binding breaks. Furthermore, binding inside the container offers limited security, as the quality of the license "anchor" is generally lower than on a bare-metal host.
The Technical Verdict: SmartBind can be appropriate for PoCs, while host-bound licensing is recommended for production.
CmCloud for SaaS: Identity-Centric Licensing
![]() As ISVs shift toward subscription-based SaaS models, the traditional machine-binding model can become limiting. CmCloud effectively redefines the "container" by moving the license identity to a secure Wibu-Systems cloud server.
As ISVs shift toward subscription-based SaaS models, the traditional machine-binding model can become limiting. CmCloud effectively redefines the "container" by moving the license identity to a secure Wibu-Systems cloud server.
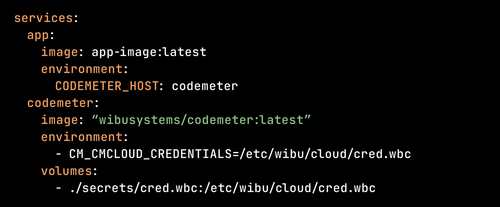
The Concept: The application container no longer holds a license; it carries a Credential. This credential acts as a secure key to a specific CmCloudContainer hosted in the cloud.
- Complete Decoupling: The license follows the instance or user rather than being bound to specific hardware. Containers can be killed and recreated across hundreds of different hosts without re-activation.
- High Awareness: ISVs gain real-time visibility into license usage, enabling data-driven decisions on feature adoption and seat allocation.
- SaaS-Ready: Aligns naturally with modern web-based deployments where "hardware" is a fluid concept.
- The Trade-off: Requires a persistent Internet connection to maintain the cryptographic "heartbeat" with the cloud server.
The Reference Architecture: Decoupled Network Licensing
For on-premise Docker or Kubernetes clusters, it is advisable for the license to reside outside the application container. This creates a "Stateless App / Stateful License" architecture.
- Resilience: If a container is rescheduled by an orchestrator, it simply re-establishes a connection to the Network Server.
- Separation of Concerns: The application image remains focused on business logic; the CodeMeter License Server (on the host or a separate VM) manages the cryptographic state.
Edge Computing: Establishing a Root of Trust
In Industrial IoT (IIoT), you must protect IP on decentralized hardware. The Hybrid Host Model represents a widely adopted technical approach: the CodeMeter Runtime is installed on the Host OS, and containers access it via an internal network bridge.
Path A: Hardware-Bound Virtual Licenses
![]() Best for mass-scale deployment on standardized hardware. The license is bound to the physical machine’s fingerprints but managed as a secure file on the host. This combines "soft" delivery with "hard" host-level security.
Best for mass-scale deployment on standardized hardware. The license is bound to the physical machine’s fingerprints but managed as a secure file on the host. This combines "soft" delivery with "hard" host-level security.
Path B: CmDongle and CmASIC (the Physical Enclave)
![]() For high-assurance security, a physical hardware enclave is used. CmASIC is integrated into the printed circuit board (PCB), while CmDongle provides USB or SD card-based hardware. The host Runtime manages the communication with the chip, while the containerized app consumes the license via the internal bridge, ensuring cryptographic keys never leave the silicon.
For high-assurance security, a physical hardware enclave is used. CmASIC is integrated into the printed circuit board (PCB), while CmDongle provides USB or SD card-based hardware. The host Runtime manages the communication with the chip, while the containerized app consumes the license via the internal bridge, ensuring cryptographic keys never leave the silicon.
Strategic Guardrails: Recommended ISV Practices
- DON'T bind virtual licenses inside the container. Always set up virtual licenses on the Host OS to ensure a high-quality, stable binding.
- DON’T mount USB devices directly to the application container. Set up a license server on the host and access licenses via network connection.
- DO leverage CmCloud for friction-free scaling in connected environments.
- DO leverage network licenses for maximum flexibility in air-gapped environments.
- AVOID high-frequency activation cycles. Do not re-activate SmartBind licenses for every ephemeral container spin-up.
Licensing as an Enabler
In a containerized world, licensing should not be viewed merely as a hurdle, but as a strategic layer of the application architecture. By moving away from potentially fragile internal container bindings and toward decoupled network or cloud models, ISVs can provide the flexibility their customers demand while maintaining the security their business requires. The objective is to achieve a "Protection-by-Design" approach where the license is as scalable and portable as the code it protects.
KEYnote 51 – Edition Spring/Summer 2026